The Shift in Cryptography
The foundation of internet security rests on specific mathematical assumptions - problems that are computationally infeasible for classical computers to solve. However, the theoretical boundaries of computing are expanding rapidly. Quantum computers represent a shift that will eventually make our current asymmetric encryption methods obsolete.
Powerful quantum computers might be a some time away. But the threat is real today. Hackers use a "Harvest Now, Decrypt Later" strategy. They record your encrypted traffic, VPNs, and backups right now and they store this data to decrypt it later. Do you have data that must stay secret for ten or twenty years? If so, quantum computers put you at risk and you need to overthink your encryption mechanisms.
Luckily, the transition to quantum-resistant security is already underway. Cloud providers like AWS are deploying post-quantum cryptography (PQC) across their services, enabling organizations to future-proof their infrastructure.
The Defensive Strategy in AWS
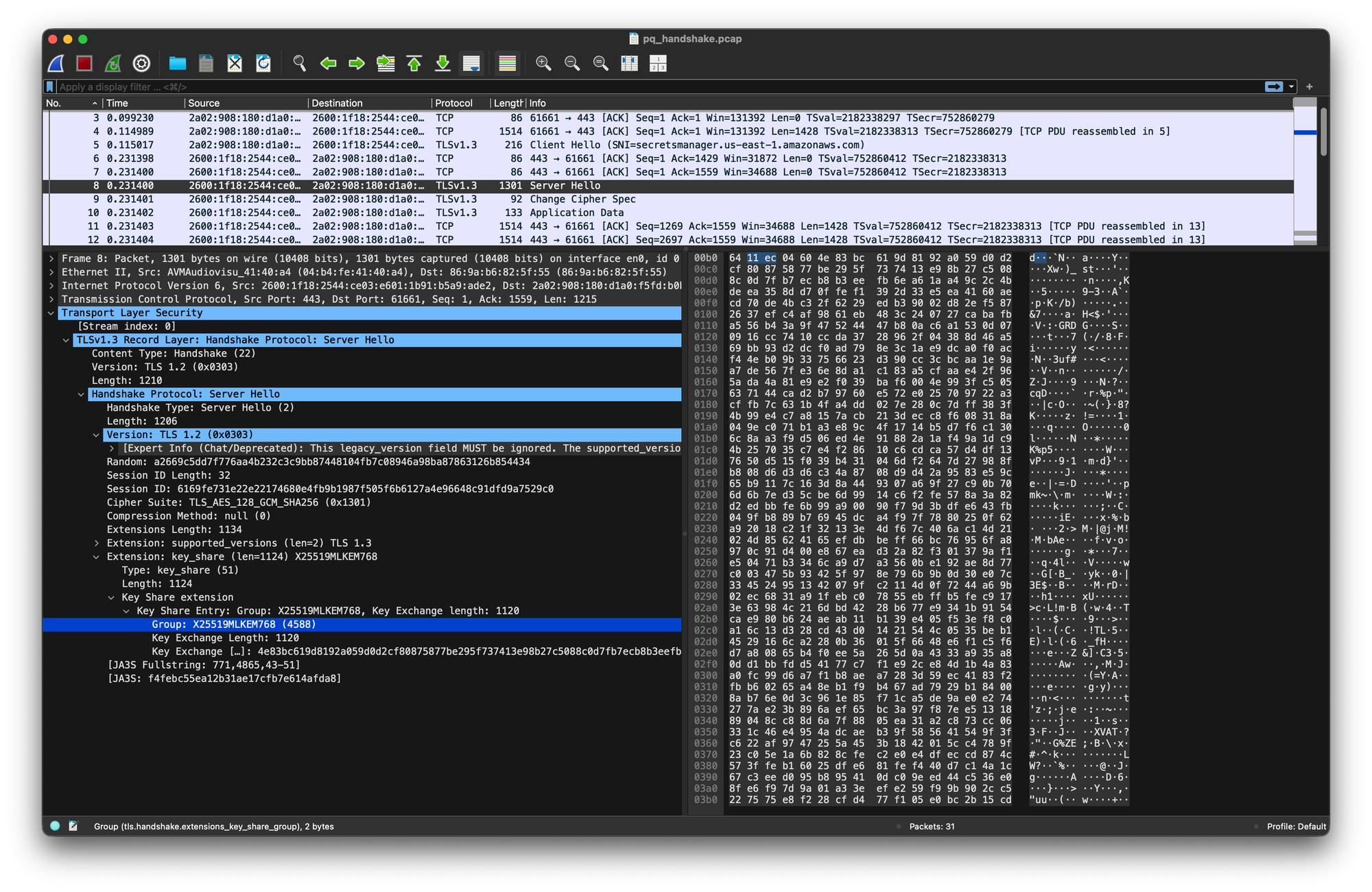
Transitioning entirely to new cryptographic standards carries inherent risk, as lattice-based algorithms have not undergone the decades of adversarial testing that RSA and ECC have. To mitigate this risk, AWS employs a Hybrid Approach.
A hybrid TLS handshake uses a classical algorithm and a post-quantum algorithm together. An attacker must break both to decrypt your session. If the new algorithm fails, the old one protects you. When quantum computers break the old encryption, the new algorithm holds the line.
Securing the Perimeter with Load Balancers
The most immediate action you can take to protect against "Harvest Now, Decrypt Later" attacks is updating the security policies on your Application Load Balancers (ALB) and Network Load Balancers (NLB).
By selecting a security policy with "PQ" in the naming convention (such as ELBSecurityPolicy-TLS13-1-2-Res-PQ-2025-09), your load balancer will automatically negotiate hybrid post-quantum TLS with any compatible client. If a client does not yet support it, the connection gracefully falls back to classical TLS.
Auditing with AWS Config
How do you find your "vulnerable" load balancers? You can automate discovery using AWS Config. Use the advanced query feature to find all TLS/HTTPS listeners:
SELECT
accountId,
resourceId,
configuration.protocol,
configuration.sslPolicy
WHERE
resourceType = 'AWS::ElasticLoadBalancingV2::Listener'
AND configuration.protocol IN ('HTTPS', 'TLS')This simple query returns your entire perimeter. You can then quickly sort the configuration.sslPolicy column in the console. This shows which listeners lack a quantum-resistant policy.
A Zero-Risk Migration
Security engineers fear changing TLS policies. Nobody wants to break legacy clients. However, adding a PQ policy carries zero risk. AWS negotiates the best protocol that the client and server both support. If an older client connects, the ALB falls back to classical TLS. This guarantees backward compatibility.
Protecting Long-Lived Signatures in KMS
Data-in-transit benefits from hybrid TLS. Digital signatures present a different challenge. You might sign IoT firmware or legal records. Those signatures must remain secure for decades. A quantum computer could forge a signature to spoof a software update.
AWS Key Management Service (KMS) now supports ML-DSA keys. Transition your long-lived signing operations to ML-DSA. This ensures your digital signatures remain valid mathematically long after quantum computers arrive.
Why Current Encryption Fails?
To understand the severity of the quantum threat, we must look at the mathematics underpinning modern encryption and why quantum computers break these specific paradigms.
Symmetric Encryption
In symmetric encryption, the same key encrypts and decrypts data. AES-256 is the standard. Quantum computers can attack symmetric encryption using Grover's algorithm. But this only yields a small speedup. It reduces AES-256 to roughly 128-bit security. Since 128-bit security is still strong, your symmetric data remains safe. You do not require re-encrypt your data at rest.
Asymmetric Encryption
The true vulnerability lies in asymmetric encryption, which relies on a public and private key pair. Asymmetric encryption is essential because it solves the key distribution problem, allowing two parties to establish a secure connection over an untrusted network. It forms the backbone of TLS handshakes, digital signatures, and certificate verification.
The security of asymmetric encryption depends on the sheer difficulty of certain mathematical operations:
RSA (Rivest-Shamir-Adleman) relies on integer factorization. You choose two massive prime numbers (p and q). You multiply them to create a huge number (n). The public key uses n. The private key needs p and q. For a classical computer, factoring n back into p and q takes years.
ECC (Elliptic Curve Cryptography) relies on the discrete logarithm problem over elliptic curves. You have a starting point P and a final point Q on a curve. It is nearly impossible to find the scalar k that moves P to Q. Like RSA, working backward is too hard for traditional chips.
In 1994, Peter Shor proved computers could crack these math problems. A large quantum computer can solve factorization and discrete logarithms in hours instead of years. By leveraging quantum superposition to explore multiple states simultaneously and quantum interference to amplify the correct answer. Once a quantum computer reaches the necessary scale, RSA and ECC will be broken.
The Post-Quantum Encryption Solution
To stop this, we need new cryptography. We need problems that resist quantum attacks.
In 2024, NIST approved the first post-quantum standards. These move away from old math. Instead, they use lattice-based cryptography.
- ML-KEM (FIPS 203): A Key Encapsulation Mechanism. It replaces Diffie-Hellman and ECDH. Security relies on finding the shortest non-zero vector in a massive lattice. Its security relies on the difficulty of finding the shortest non-zero vector in a high-dimensional lattice lattice.
- ML-DSA (FIPS 204): A Digital Signature Algorithm. It replaces RSA and ECC.
Architectural Recommendations
Security engineering means prioritizing risks and mitigating them with the best fitting solution.
- Focus on Long-Term Confidentiality: Session tokens like JWT lose value quickly. They do not need an immediate overhaul. Focus on data with a ten-year shelf life. You can automate the discovery of sensitive data using AWS Macie to prioritize encrypted repositories.
- Leave S3 Encryption Intact: Do not waste time re-encrypting data at rest. AES-256 is safe. Focus instead on the asymmetric handshakes.
- Audit Your Trust Anchors: Find digital signatures with an expiration date beyond 2030. Migrate those processes to ML-DSA.
Cryptography is evolving. However, the core principles of AWS cloud security remain the same.
Frequently Asked Questions
Q: Do I need to re-encrypt all my Amazon S3 buckets to be quantum-safe?
A: No. Data at rest uses symmetric encryption like AES-256. AES-256 is quantum-resistant. The real vulnerability lies in how keys move in transit.
Q: Will updating my ALB to a "PQ" TLS policy break connections for older clients?
A: Absolutely not. The "PQ" security policies use a hybrid approach. If a client does not understand ML-KEM, the load balancer falls back to classical TLS. The migration blast radius is zero.
Q: When will quantum computers break encryption?
A: Estimates range from 2030 to 2045. However, adversaries use "Harvest Now, Decrypt Later" tactics. You must act today if your data holds long-term value.
Q: Are ML-DSA keys more expensive in AWS KMS?
A: No. AWS prices ML-DSA keys the same as standard keys at $1 per month. But the signatures require more bytes. They consume slightly more bandwidth during transmission.






Member discussion